A 3,000-page batch of internal communications from the RCMP obtained by The Tyee provides a window into how the force builds its capabilities to spy on internet users and works to hide its methods from the public.
The emails and documents pertain to the RCMP’s Tactical Internet Operational Support unit based at the national headquarters in Ottawa and its advanced web monitoring program called Project Wide Awake.
The files include an internal RCMP presentation that contradict how the force has characterized Project Wide Awake to Canada’s privacy commissioner and The Tyee in past emails. A slide labels the program’s activities “Social Media Surveillance,” despite the RCMP having denied that description applied.
Communications show one high-level officer blasting the project before leaving the RCMP for Chinese tech firm Huawei.
Other members were jokingly dismissive of public concerns about privacy violations — a training slide for the project says: “You have zero privacy anyway, get over it.”
In seeking contract renewals and wider capabilities, the RCMP claimed its spying produced successful results, including finding online a “direct threat” to Prime Minister Justin Trudeau.
The documents reveal the RCMP:
- Gained permission to hide sole-source contracts for Project Wide Awake from the public through a “national security exception.”
- Discussed “tier three” covert operations involving the use of proxies — intermediary computers located elsewhere — to hide RCMP involvement with spying activities.
- Purchased software with an aim to search “Darknet,” which it defined to include “private communications” and those from “political protests.”
- Has used a tool to unmask lists of “friends” on Facebook for users that specifically set friends’ information to private on the platform.
- Was “wasting resources, wasting time, wasting money” on IT projects, according to the then RCMP chief information officer.
- Took the names for Project Wide Awake and other internet surveillance programs from the X-Men comic book series, in which illegal government programs hunt human “mutants.”
The Tyee shared some excerpts from the files with Brenda McPhail, director of the Privacy, Technology and Surveillance Project at the Canadian Civil Liberties Association, who said they raise alarms.
“This is more evidence that we should be very concerned about this program and the incredibly secretive and unaccountable way that it was developed and run,” she said.
The Tyee first revealed in March 2019 the existence of Project Wide Awake which experts said could pose a threat to Canadians’ privacy and charter rights, and the same month filed a freedom of information request to the RCMP to find out more. The release of the files took a year and a half, following a complaint to the watchdog federal Office of the Information Commissioner. This is the first of more Tyee articles to come based on what we received.
Hiding software purchases, claiming ‘national security’
After The Tyee exposed Project Wide Awake, the RCMP said the program employed off-the-shelf social media marketing software sold to companies and agencies for uses that merited no public concern or judicial permission.
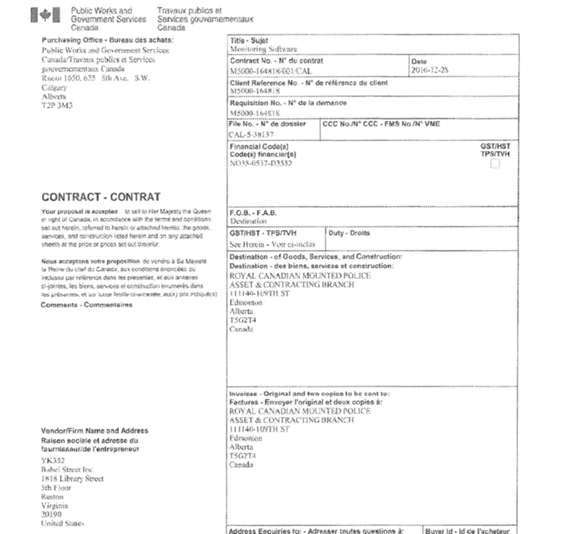
Internally, however, the force was seeking to extend licenses on more complex monitoring software geared for law enforcement called Babel X and use it ongoing in investigations across the country. The FOI documents show this had been a goal of the force as far back as 2017.
Makers of the Babel software claim it can translate 200 languages. According to a 2017 Vice article, it has “extremely precise” filters for dates, times, data type, language and even feelings and moods expressed in messages. The article quotes a since removed passage on the company’s website boasting “the ability to evaluate sentiment in 19 languages — far exceeding the capacity of any other competitor."
Several years before applying to secretly procure Babel X for wider purposes, the RCMP already employed it in parts of its operations, the documents released to The Tyee confirm.
The force had been using Babel X since 2016 in its Manitoba division. By 2018, the RCMP also used Babel X at its national headquarters in advance of the G7 meeting in Quebec, records including a contract confirm.
But the 2018 contract was approved for only one year for the G7 and had since expired, the RCMP told The Tyee in an October email.
In February 2019, as the force sought to secretly obtain Babel X or a tool much like it, an officer argued to Public Services and Procurement Canada that “if released into the public domain” knowledge such software was being used by the RCMP could “jeopardize border integrity” and “criminal and national security investigations,” and “provide avenues for adversaries to attempt to defeat these capabilities,” the newly released documents show.

Gilles Michaud, then commissioner of federal policing, made the argument while requesting a “national security exception” which would remove the buy from public procurement procedures.
The documents reveal the RCMP had previously obtained such exemptions for contracts related to Project Wide Awake as well as existing licenses for Babel X.
But it would appear Michaud did not get his way this time.
The force posted a public procurement notice on Nov. 29, 2019 for an unnamed “advanced social media tool,” reported on by The Tyee, and went on to quietly buy Babel X on Sept. 2, 2020.
‘A kind of trick’
Back on Dec. 28, 2016, the RCMP ordered “optional goods” — extra software and features — in a Babel X contract found in the documents, but the list was blanked out. No contract or procurement documents naming Babel X appeared on Public Services and Procurement Canada websites until 2020.
McPhail calls it “a kind of trick” the way RCMP downplayed the power of the Babel X software it was already using in some of its offices, and then sought to hide it from public scrutiny by gaining a national security exemption.
“We have a public crisis around police accountability and their use of surveillance technologies,” said McPhail. “That crisis is fed by this kind of trick — attempting to put procurement into categories that permit greater secrecy.”

Kate Robertson, a criminal defence lawyer and researcher at University of Toronto’s internet security-focused Citizen Lab agrees.
“The methods are either unexpected and therefore must remain secret, or their methods are ordinarily expected by individuals and therefore non-intrusive. The RCMP cannot have it both ways. The constitution draws a bright line: all intrusive surveillance practices by police services must be the subject of prior judicial oversight,” wrote Robertson in an email.
Private messages, political protests named ‘Darknet’ targets
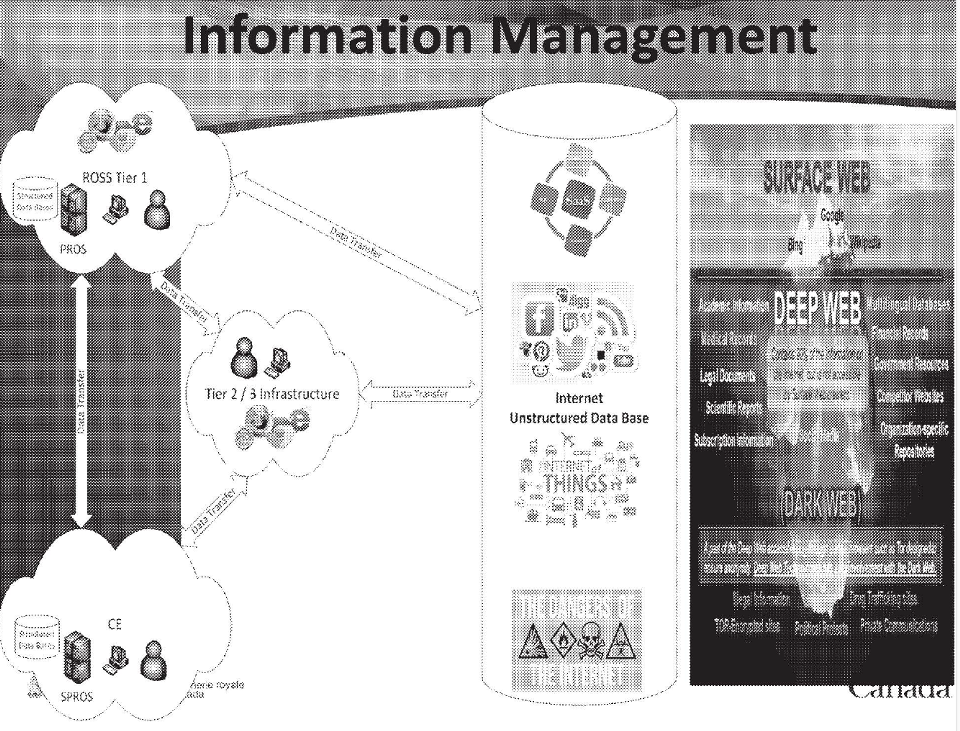
In procurement forms and presentations to RCMP trainees about who it will target with its expanded tools, the RCMP lists “Darknet,” commonly understood to refer to hidden, encrypted parts of the web.
In other documents the Tactical Internet Operational Support unit names “private communications” and “political protests” in its internal definition of Darknet, which the force aimed to target. Also listed as part of Darknet are “illegal information,” “drug trafficking sites,” and “Tor-encrypted sites” which hide user identities by moving data through different servers.
But in its communication with the privacy commissioner found in the documents, the RCMP claims the targets of its monitoring are exclusively “open source,” in this case implying the tool’s purpose is to scan communications that are posted with no expectation of privacy.
“The term ‘open source’ is vague, and can obscure a wide range of sophisticated technological interferences including even hacking,” said Citizen Lab’s Robertson.
“For this reason, even open source surveillance techniques are illegal when they impact the privacy interests of individuals in Canada.”
“The surveillance technologies that are only now being revealed do not appear to be truly open source methods,” said Robertson.
McPhail added, “Our privacy commissioner has gone on the record as saying not all information in the public domain loses all reasonable expectation of privacy.”
McPhail found troubling the documents reflect an RCMP view that any communication on the internet can be assumed fair game for surveillance because it’s already in a public realm. “It’s one thing to understand that an individual will see your passing communication, and quite another thing to assume that everything you’ve ever written will be subjected to an analysis by the state.”
“It changes the relationship between the citizen to the state, and their expectations of privacy in their communications,” said McPhail.
Another RCMP email in 2017 makes reference to a separate “dark web crawler” project being led by Eric Huot, then a member of the force. Huot now runs a private internet intelligence firm, where he claims he “developed, led and managed” the RCMP’s Tactical Internet Operational Support team for over 12 years, as well as the 2018 G7 open source intelligence unit.
Huot is listed as “Operations Lead” at the TIOS team in internal documents from May 2017.
Reached by The Tyee, Huot declined to comment on RCMP projects but stated that the interception and collection of private communications, whether from Darknet or elsewhere are “not synonymous with open source intelligence activities.”
Cracking into Facebook friends
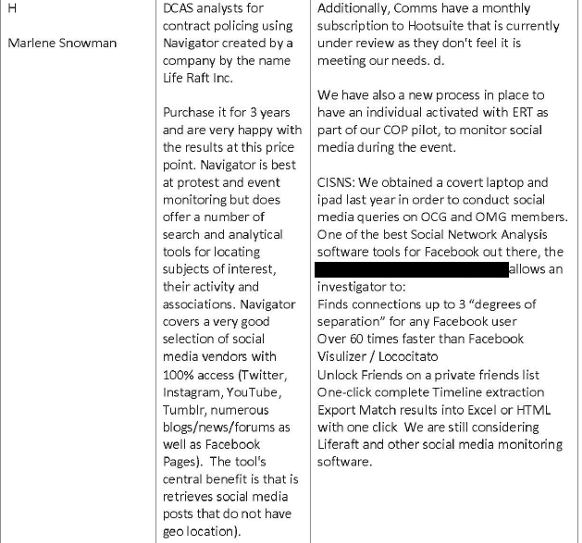
Emails in 2017 reveal the RCMP conducted a cross-province survey of software already in use for advanced social media monitoring in its divisions.
Nova Scotia RCMP responded by saying it uses a tool which can “unlock friends on private friend lists,” apparently referring to Facebook users who have set their list of friends on the platform to be hidden.
The Nova Scotia force had used software on a “covert laptop” in its investigation of organized crime and motorcycle gangs, it noted. The software also enables officers to extract entire timelines of Facebook users into Excel forms.
The force compared the tool favourably to Facebook Visualizer and Loco Citato, which perform similar functions. Loco Citato, which was also marketed to law enforcement, had been issued a cease and desist order from Facebook in 2014 for its extraction of data from the platform, according to a blog entry of its creator.
The Nova Scotia RCMP also said it used a social media scanning software named Navigator, made by Life Raft Inc., for “protest and event monitoring.”
Tiers of secrecy
The documents obtained by The Tyee reveal that the RCMP’s Tactical Internet Operational Support unit codes its internal operations according to how much it wants each hidden from view.
Tier 1 operations can be visible to the public.
Tier 2 operations, described as “low attribution,” are those for which it is considered not a serious problem if they exposed.
Tier 3 operations are considered covert or undercover and involve separate clearance and clear guidelines to ensure the RCMP is not identified.
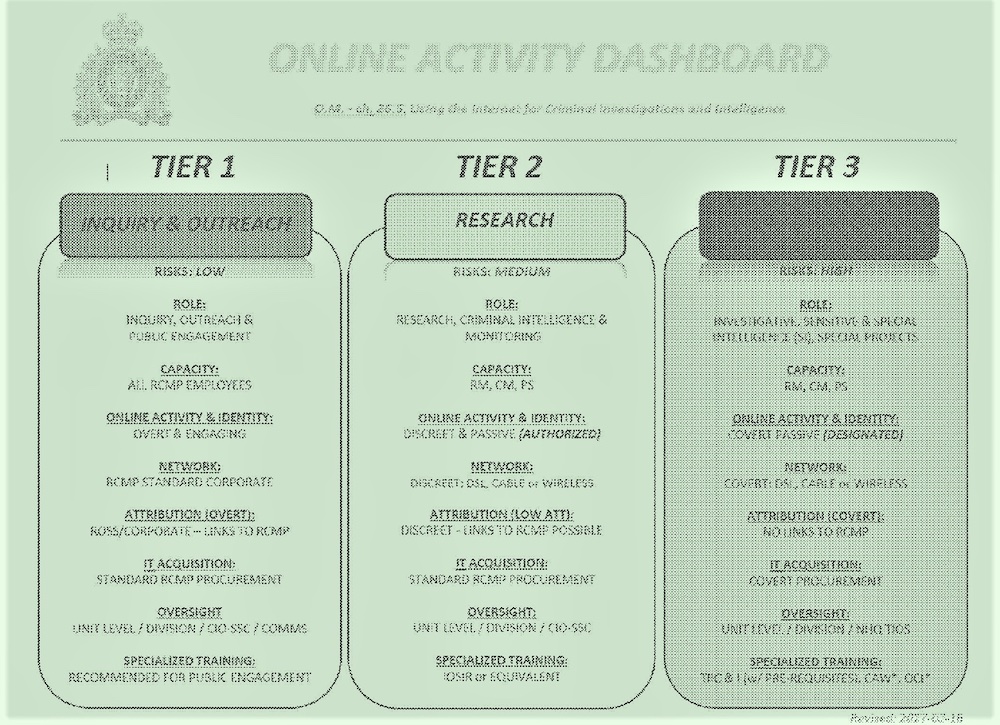
RCMP meeting notes show members discussing using technologies to enable its computers and cell phone activity to appear to originate in other countries “instead of bouncing all signals out of Ottawa.”
Heated words and a top officer exits
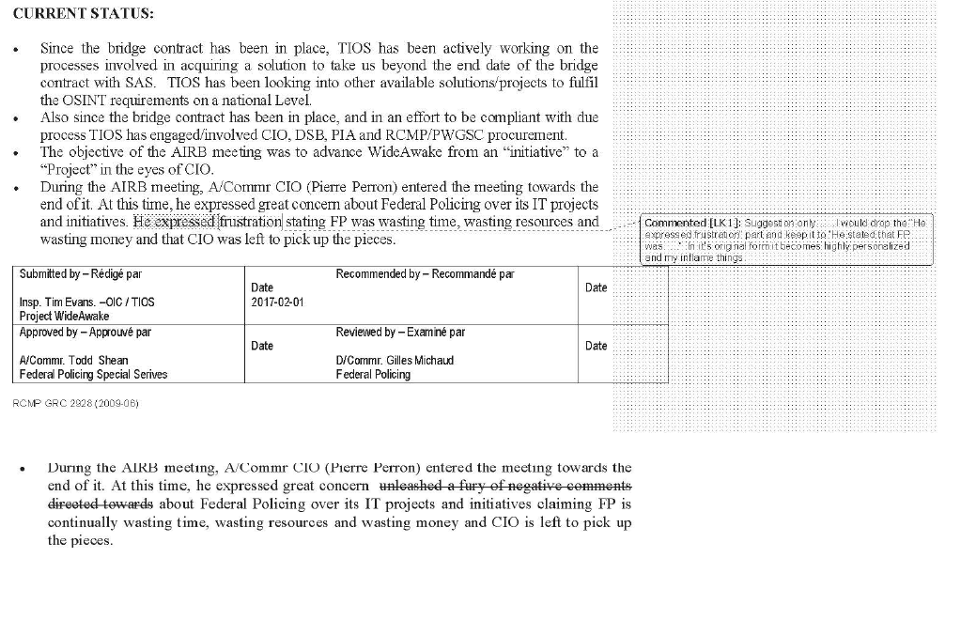
On Jan. 31, 2017, the RCMP discussed projects of the Tactical Internet Operational Support unit in a strategy meeting. A draft of a briefing note prepared by Tim Evans, officer in charge of Project Wide Awake for the deputy commissioner of the RCMP, suggests high tensions in-house.
The then chief information officer of the RCMP, Pierre Perron, entered the meeting late and “unleashed a fury of negative comments” directed at Federal Policing — the national division of the force running TIOS and Wide Awake — over its internet technology projects, said Evan’s draft, included in an email.
Federal Policing is “continually wasting time, wasting resources and wasting money and [Perron] is left to pick up the pieces,” wrote Evans in an account of Perron’s comments at the meeting dated Feb. 1, 2017. Perron would be speaking to the deputy commissioner, Evans added.
An officer whose identity is unclear commented that the wording in Evans’ draft was “highly personal” and might “inflame tensions” with Perron.
In the briefing, Evans wrote that the objective in TIOS remains to “make sure we follow the processes of the organization in order to not have another incident which caused [Perron] to express the frustration with Federal Policing.”
The unknown second officer said Evans “makes it sound like we do work to placate” Perron. And asked, “Would not the objective be to follow a process that advances Wide Awake in a legal and policy compliant manner?”
Barely a month after the meeting, Perron had departed the force and accepted a job at Huawei, according to his LinkedIn profile. The move was controversial since Perron possessed secrets about Canadian government and RCMP operations. Canada is facing pressure to ban Huawei’s attempt to develop 5G networks because of the company’s close ties to the Chinese Communist Party.
Huawei “has had a very aggressive campaign to soften its image,” Chris Parsons of Citizen Lab told the Globe and Mail a month after Perron moved to join the company. “Having a high-level Mountie might be sufficient moral suasion to alleviate some of the concerns,” Parsons added.
“I am well versed on my obligations under the Security of Information Act,” said Perron in the same Globe piece.
Reached by The Tyee via email, Perron asked to see the documents in order to comment but did not reply further after receiving them.
A police culture that draws on comic books
Project Wideawake was the name given in the X-Men comic book series to a secret, illegal government program designed to hunt down mutants — humans with special powers.
A fan website Marvel Database explains Project Wideawake “denied mutants even their most basic civil rights.”
Prior to The Tyee’s reporting on the RCMP’s web spying tools, the only online matches for the words “Project Wideawake” could be found on such X-Men fan pages.
Other covert program names at the RCMP Tactical Internet Operational Support unit borrow X-Men terminology about tracking mutants.
“It’s not uncommon for individuals who deal with dark subject matter to attempt to maintain mental equilibrium through the use of dark humour,” noted the CCLA’s McPhail. “That’s a recognized coping strategy.”
The documents make reference to TIOS aims to track organized crime and biker gangs, witness protection programs and terrorist threats.
However, she added, “It’s odd to me that our national police force would compare themselves to mutant hunters in a comic book universe. Particularly when we understand that one of the uses of this technology was to look for signs of unrest around constitutionally protected protest.”
Dark humour may inflect a slide in a presentation meant to orient RCMP members to Project Wide Awake. It declares: “You have zero privacy anyways, get over it.”
But in other moments, the force earnestly justifies its secret web surveillance by invoking a sense of overriding public duty.
“If I was to keep my community safe, I had to know who they were,” training materials for Project Wide Awake quote former RCMP commissioner Bob Paulson comparing his early career patrolling Chilliwack, B.C. to monitoring activity on the web.
Claims of serious threats intercepted
“Project Wide Awake uses commercially available software to analyze information posted on public social media platforms, work that requires no search warrant,” the RCMP told The Tyee when it first reported on the program last year.
But an exchange between a covert operations officer acknowledged in an internal RCMP exchange that Project Wide Awake is a “social media application software tool [that] could be considered surveillance by the public.”
In the same document — a form used to determine whether a privacy impact assessment should be required — the covert operations officer checked off that Project Wide Awake would not “use or disclose more personal information than in the past... collect the personal information directly from the subject individual,” or “collect personal information from other programs” from within the RCMP or “from other institutions, from other governments or from the private sector.”
The officer affirmed that Project Wide Awake data “would be used in decision-making processes that directly affect individuals.” But its collection “is specific to intelligence or investigative requirements,” the officer noted.
The internal documents obtained by The Tyee include “success stories” the RCMP cited in its proposal to obtain funding for renewal of its software licenses. Listed:
“February 2018: A request was received from C Division to see if the WideAwake tool could be used to obtain historic Twitter data from the SOC [subject of concern] relating to the Quebec Mosque shooting.”
“March 2018: The tool surfaced a tweet by an individual threatening to shoot up a high school. The TIOS team was able to determine that the individual resided in Florida.”
“March 2018: The tool surfaced a direct threat to the life of Prime Minister Trudeau. This was the Threat Assessment Unit who identified the threat using the tool.”
The RCMP has been in the process of completing a federal privacy impact assessment for over a year.
The Tyee has contacted the RCMP for comment on aspects of the released documents, including privacy protections, secrecy and how its web surveillance fits into investigations, and will include its responses in future pieces.
Read more: Rights + Justice, Science + Tech















Tyee Commenting Guidelines
Comments that violate guidelines risk being deleted, and violations may result in a temporary or permanent user ban. Maintain the spirit of good conversation to stay in the discussion.
*Please note The Tyee is not a forum for spreading misinformation about COVID-19, denying its existence or minimizing its risk to public health.
Do:
Do not: