Facebook promised last month it had fixed a “bug” in its platform that could allow someone to send a unique ad to exactly one intended user who is unaware they are the only recipient — a controversial practice called sniper-targeting.
But the capability still exists, The Tyee has proven.
Does that matter? Yes, on several levels. Sniper-targeting threatens your personal privacy, your ability to gauge what is real and fake online, and even the health of democracy. And in Canada, it may be illegal.
The related, less exacting practice of “micro-targeting” has been criticized for its ability to sow political division by inflaming prejudices in a highly strategic way.
Political micro-targeting must stop, urged Britain’s Institute of Practitioners in Advertising, an industry organization. Its president, Sarah Golding, told the New York Times, “There is a danger that every single person can get their own concerns played back to them.”
But sniper-targeting, a distilled and potentially more powerful version of micro-targeting, has received much less scrutiny.
From micro to solo
It’s the aim of advertisers to be able to match their pitches as closely as possible to the desires and anxieties of their customers. Facebook, Google and other social media platforms have built their business models on delivering such matches — while pledging anonymity to users.
Facebook and others do this by connecting batches of online users to ad clients. These batches can be made up of people who share characteristics such as geographic location, political leanings, hobby enthusiasms, shopping patterns, etc.
They can be chosen by Facebook itself. Or someone who wants to advertise on Facebook can assemble their own list of specific people and show an advertisement to the group via Facebook’s “custom audience” feature.
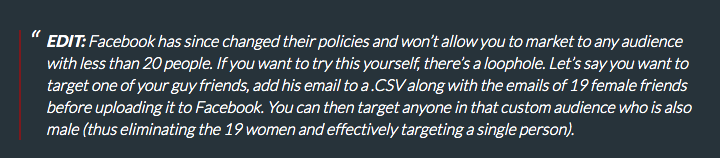
What is the minimum size of these batches? No smaller than 1,000 at a time, Cambridge Analytica cofounder Christopher Wylie and Facebook itself assured a Canadian parliamentary committee. Facebook’s developer guidelines cite a lower figure of 100, however, and Facebook has confirmed to The Tyee the number could go as low as 20.
Micro-targeting, as this practice is called, preserves Facebook user anonymity because each ad recipient is part of an aggregate whole, and it’s the statistics from the whole that are shared with the client.
There is a sharp line, therefore, between micro-targeting and sniper-targeting. The latter is so precise it allows advertisers to zero in on an individual, and record the targeted person’s online actions in response to the ad. No social media outlet, including Facebook, admits to knowingly enabling sniper-targeting.
And yet, The Tyee — for a second time — has run an experiment and proven such sniper-targeting is possible on Facebook.
Provided with evidence of this by The Tyee, Facebook did not confirm the “bug” still exists but said it is looking into it.
An open secret for five years
Since at least 2014, people on the web have posted instructions, easily Googled, explaining how to exploit Facebook’s advertising platform in order to sniper-target individuals. One such guide has been viewed over a million times. The method revealed can be used in various ways to violate privacy and wield disinformation.
For example, sniper-targeting can be used to send customized messages to a single person — perhaps an influential decision maker — in order to fool them.
In an episode of the TV show The Good Fight, for example, a plucky legal aid creates an advertisement for a fake art show and beams it only to one judge, who is ruling whether an undocumented immigrant is a noted artist and so should be granted a visa. That’s just fiction you say?
U.K. Labour leader Jeremy Corbyn’s own staff targeted political ads to him which he thought were seen by everyone, so that he would think his team was following his directions on messaging. The party chiefs engaged in this subterfuge because they hated the ads Corbyn wanted to use.
In a piece published on Medium, ad agency owner Michael Harf brags about a related tactic. He urges marketers use sniper-targeting to push an unwitting possible customer into sealing a deal.
Once a salesperson has gathered enough information from the potential client to know they are on the fence about making a financial decision, the company can tailor an ad exactly for the prospect. And when that customer sees it, they may assume the company has a big ad budget, or has a sale going on, or whatever the company feels might trick the potential buyer into making the leap.
Reached by The Tyee, Harf did not answer questions about the ethical and practical aspects of his recommended method.
Sniper-targeting also is a dream for anyone bent on fomenting discord and amplifying fake news.
The flip side of sniper-targeting is that it allows the marketer to collect personal data about a single person’s activities online including their location while browsing on Facebook, secretly violating the norms of privacy a user of Facebook is given to assume.
That means sniper-targeting might even enable someone with intent to blackmail.
Public inquiry left out sniper-targeting
Members of Canada’s Parliamentary Committee on Access to Information, Privacy and Ethics wanted to know about the risks and scope of micro-targeting, as used by Cambridge Analytica to sway elections.
In those hearings, conducted last May, data-mining whistleblower Christopher Wylie explained: “The problem with targeting is that rather than standing in that public forum, you are going to each individual voter and whispering something in their ear. Now, in many cases what you’re whispering is something you would be happy to say in that public forum. In some cases, it may not be.”
MP Nathaniel Erskine-Smith asked in reply, “How narrow is the custom audience? To that point about whispering in one person’s ear, custom audiences can be drilled down to what... a custom audience of one?”
“Facebook limits the audience to 1,000,” said Wylie.
“OK,” replied Erskine-Smith.
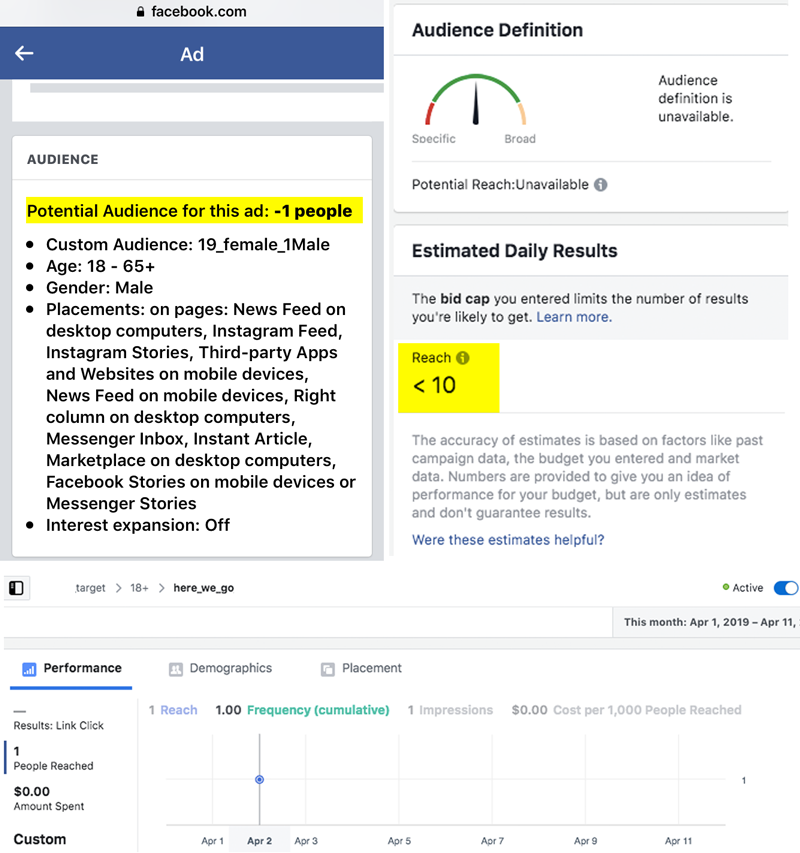
But early last month The Tyee proved Facebook’s self-service advertising platform could be manipulated to sniper-target custom ads to just one person. Facebook acknowledged the problem and then said it had been fixed.
Last week The Tyee ran another test and was successful at sniper-targeting an individual using the same methodology Facebook said was now fixed, a day before it announced a new privacy focused vision.
When Facebook representatives spoke to Erskine-Smith’s Parliamentary committee last year, they “were adamant,” he told The Tyee, “that there was no way to target individual users.” He said he would raise the issue again with Facebook soon. “We expect to have them back before us at some point this spring.”
A representative from Erskine-Smith’s office following up on The Tyee’s report confirmed they found another well-publicized case of sniper-targeting dating back to 2014.
In a story shared online, Brian Swichkow sent a sniper-targeted lone ad based on intimate knowledge of his roommate that only he could know, creeping out the roommate until he confessed.
The methodology The Tyee found still works today is the same one shared by Swichkow on Reddit in 2014 — a post detailing how to defeat Facebook’s minimum audience size safeguards and reach just one person. The tip went viral, as Britain’s The Observer noted in 2015. By then the Reddit post had over one million page views and was also featured on Adweek, Al-Jazeera, and Business Insider
Yet Facebook, and Wylie, years afterwards maintained they were not aware of the loophole.
Denial, then a ‘bug’ claimed fixed
After The Tyee first proved in March of this year that sniper-marketing could be carried out on Facebook by demonstrating an audience of one it approved, the social media corporation dismissed the finding, saying the advert wouldn’t actually deliver. But when The Tyee ran an ad and documented an impression and click, successfully traced onto our test website, the company admitted The Tyee was correct. Spokespeople said a “bug” in the system had been fixed since, and there was no evidence the technique had been used by anyone else.
The Tyee then presented Facebook with evidence of others using sniper-targeting, including live screenshots from Harf’s ad agency and commentary from Facebook experts on forums viewed thousands of times. Facebook revised its position to say nobody had used the ability to sniper-target “maliciously.” The social media giant did not explain how it knew that.
Over a month later, on April 11, The Tyee ran another test and informed Facebook the “bug” still existed. The company responded on April 16 that it was still looking into the matter.
Facebook in other circumstances has been slow to close off weak privacy measures once publicized. In some cases major clients were benefitting, while Facebook collected their ad dollars.
Facebook, for example, has been caught providing special extensions to companies including RBC, Spotify, and Netflix, enabling them to gain privileged Facebook user data — even after a public backlash caused Facebook to close the abilities off to most companies.
And the loophole that enabled Cambridge Analytica to glean a massive database of 87 million profiles from a fraction as many app users was left open for a year after Facebook identified it as a problem.
AggregateIQ had sniper-targeting tools: Vickery
The Tyee spoke with security researcher Chris Vickery about how micro-targeting and sniper-targeting can be used by firms paid to help political players sway citizens. Victoria-based Aggregate IQ is one such company, and worked closely with Cambridge Analytica to successfully push for Brexit (the U.K.’s decision to break with the European Union) and a Trump presidential victory.
Vickery discovered the tools used by AggregateIQ sitting accidentally out in the open for months for anyone to find — including credentials that would allow anyone to target the company’s massive databases of potential voters. Vickery provided key testimony about the tools and their architecture to U.K. and Canadian parliaments investigating the company’s breach of personal information.
Vickery told The Tyee that the tools gave AggregateIQ the ability to zero in on just one person, contrary to assurances to Canadian lawmakers by Wylie and Facebook.
“The stone-cold evidence would likely be with the U.K. Information Commissioner’s office, as they took physical possession of [Cambridge Analytica’s] servers,” Vickery, a researcher at security firm UpGuard, told The Tyee.
Vickery said the files he has from AggregateIQ’s software contain “scripts that say they can target individuals.”
Scripts are sets of instructions for computers which enable the process launching ads to be automated on a large scale. This, coupled with the sniping loophole, makes it possible to test hundreds of versions of ads on a single sniper target until a desired response is achieved. When the person clicks, the ad could be judged as effective. Vickery compared the process to unconsented laboratory experiments.
Sniper-targeting can also strip away a targeted person’s anonymity on the platform and landing pages of advertisements. The advertiser can use it to know precisely who saw, clicked, and is landing on their website from an advertisement. The advertiser can then further tailor what it “whispers into the ear” of the lone target.
The target’s IP address, location, type of device and browser and who they are, will all be known to the advertiser since they are the only person who could have seen and clicked the ad. Anything the target enters on the website, under an assumption of anonymity, will be known to the advertiser.
Consider an advertisement for a personality quiz asking for intimate details. The person seeing the ad may consider themselves to be anonymous when landing on the site, having never entered identifying information. The website hosting the quiz, who also placed the Facebook ad which appeared to have been broadcast to a group, knows who is on the quiz from the second they land, in addition to their location, details about their device and anything they enter on the quiz site.
Sniper-targeting likely violates law
Sniper-targeting is likely illegal in Canada, said another member of the Canadian parliamentary committee that probed Facebook, NDP MP Charlie Angus.
Angus told the Tyee back in March that targeting individuals may violate Facebook’s “terms of use.”
Companies violating those terms of use by circumventing Facebook’s minimum target sizes would be in violation of the “consent” principle of the Personal Information Protection and Electronic Documents Act, said Angus.
“If we have evidence of this, I will be asking the privacy commissioner to launch an immediate investigation,” Angus said when the Tyee first discovered the loophole.
Facebook did not answer when The Tyee asked how many people had been the lone targets of campaigns on its platform, or whether such targets will be notified that their activity and information may have been compromised by the practice. ![]()
Read more: Rights + Justice, Science + Tech

















Tyee Commenting Guidelines
Comments that violate guidelines risk being deleted, and violations may result in a temporary or permanent user ban. Maintain the spirit of good conversation to stay in the discussion.
*Please note The Tyee is not a forum for spreading misinformation about COVID-19, denying its existence or minimizing its risk to public health.
Do:
Do not: